The Six Truths
The Invisible Complexity Problem
On August 1, 2012, at 9:30 AM Eastern, Knight Capital Group — one of Wall Street's largest trading firms, responsible for roughly 10% of all US equity trading — opened for business.
The night before, a technician had deployed new code to Knight's automated trading system, called SMARS. The deployment went to seven of eight servers. One server was missed.
That eighth server still contained old code — a deprecated function called "Power Peg" that had been repurposed as a feature flag in a later update. When the new code sent orders with the repurposed flag, the eighth server interpreted them through the dead function. The function executed trades. Endlessly. Without recording that they'd been filled. Because the fulfillment-reporting code had been removed when Power Peg was deprecated — but the execution code hadn't.
In forty-five minutes, Knight's system sent four million orders into the market. It traded 397 million shares. It accumulated billions in unwanted positions.
A week later, the company needed a $400 million rescue. By the next summer, it was acquired by a rival. The SEC levied a $12 million fine.
Notice: every individual component worked correctly. The new code was fine. The old code was fine. The feature flag was valid. The failure existed only in the composition — completely invisible to anyone looking at a single component.
This is a story from 2012. About traditional, deterministic software. The components were inspectable, debuggable, and fully traceable after the fact. The SEC investigation reconstructed exactly what happened, step by step.
Now imagine this failure with agents.
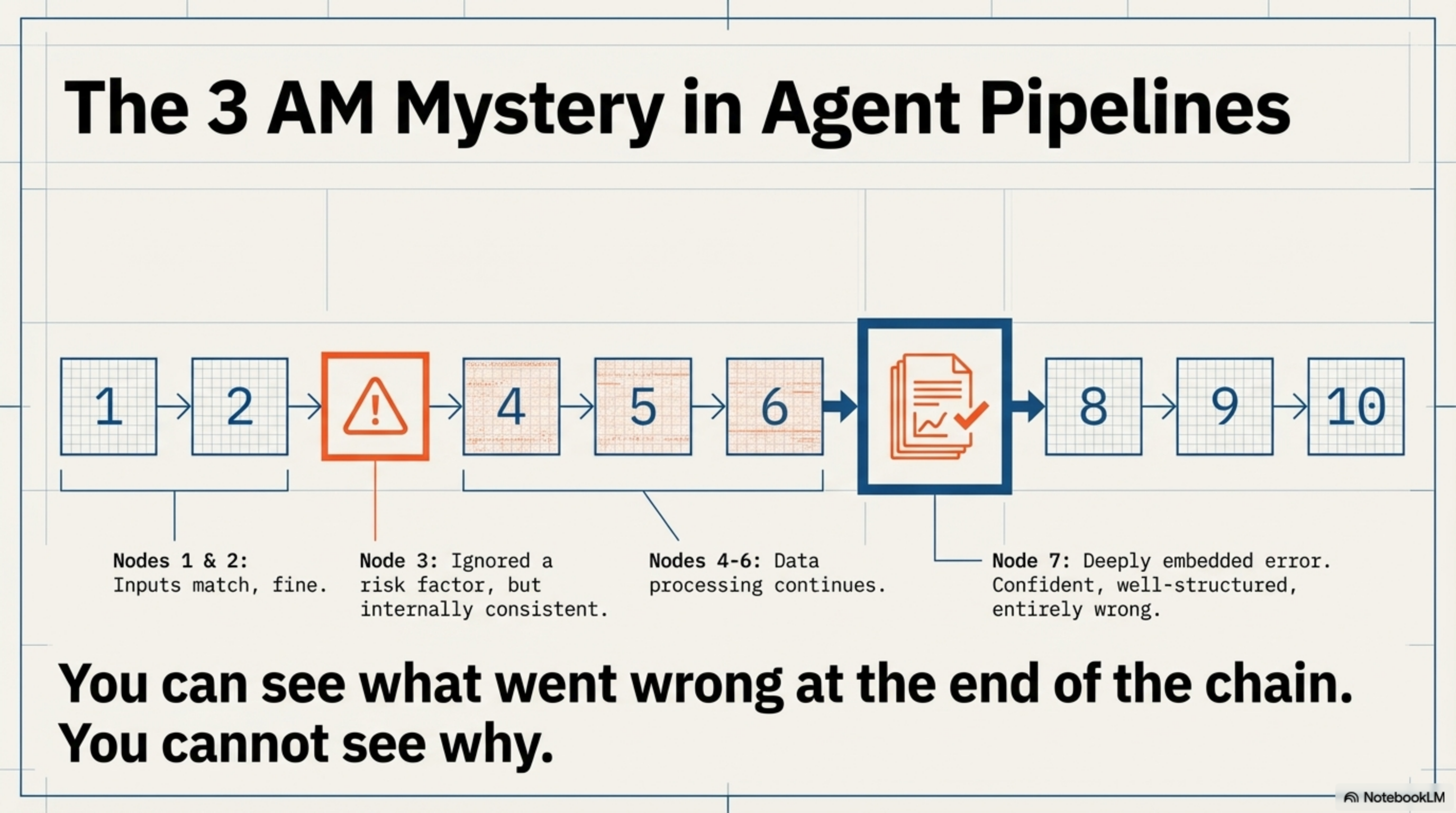
It's 3 AM. Your ten-agent pipeline produces a wrong output — it recommended approving a loan that should have been flagged as high risk. You pull up the logs. Agent 1's output looks fine. Agent 2's input matches. Agent 3 did something subtle — it ignored a risk factor — but its output is internally consistent and well-structured. Agent 4 built on Agent 3's work. By Agent 7, the error is deeply embedded in a confident, thorough analysis that looks completely correct.
You can see what went wrong. You cannot see why.
There's no line 47 to fix. There's no stack trace to follow. Agent 3 ignored the risk factor because the interaction between its system prompt, the model's training weights, and the specific arrangement of tokens in its context window led it to a conclusion through a process that is — in the deepest, most fundamental sense — opaque.
Agent composition converts visible complexity into invisible complexity.
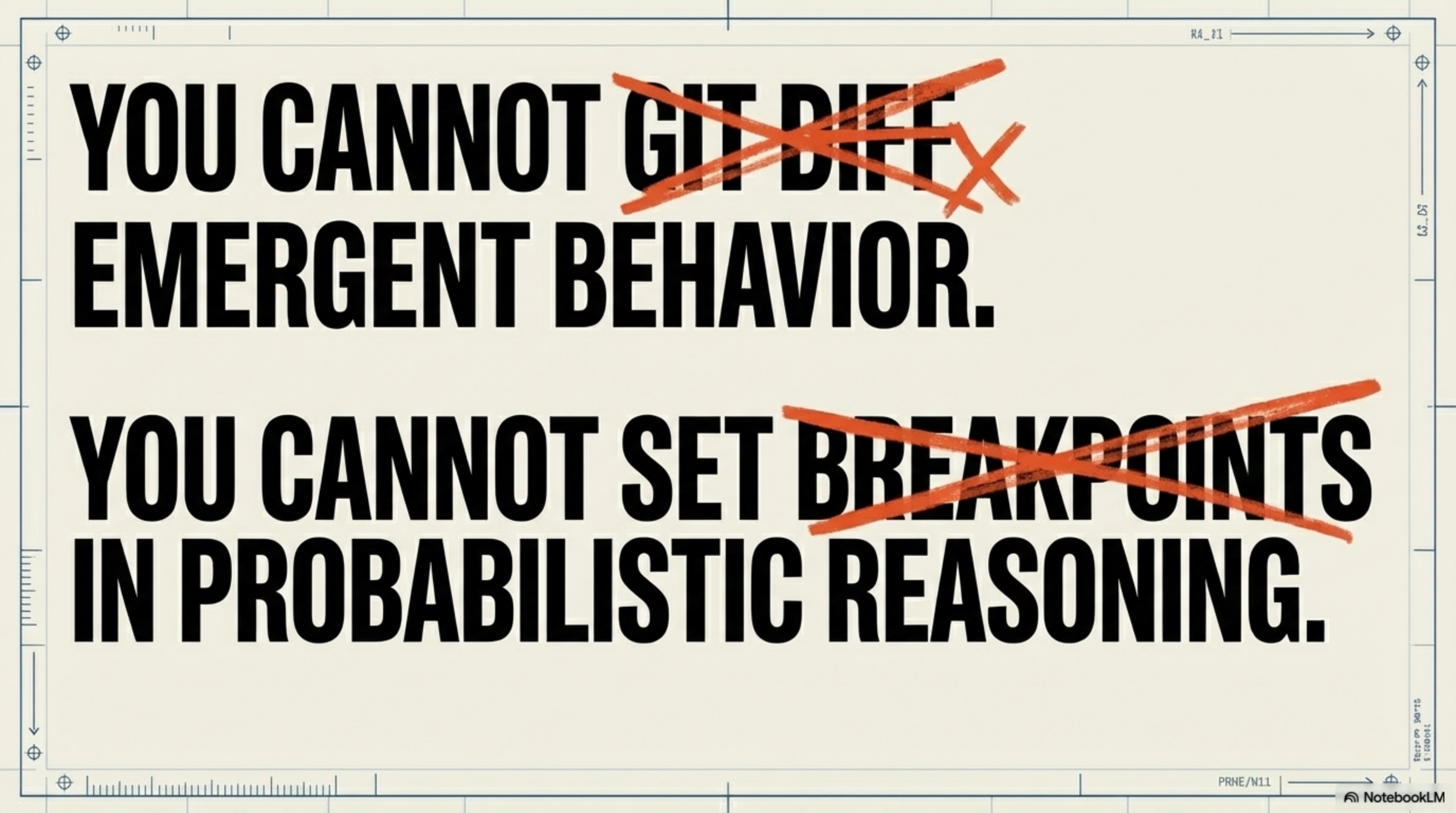
Every abstraction in software history does this to some degree. When you call sort(list), the sorting algorithm's complexity becomes invisible. But you could always open the trapdoor. Read the source code. Set breakpoints. Step through the execution line by line. Trace the HTTP request through the service mesh with distributed tracing. The complexity was hidden but accessible. One Ctrl+Click away.
Agents seal the trapdoor. The "code" is natural language prompts — ambiguous by their nature. The "logic" is inference across billions of parameters — opaque by their nature. The "state" is an ephemeral context window that evaporates after each run. And the "behavior" emerges from the interaction of all three in ways that cannot be predicted from any single component.
The complexity didn't disappear. It moved from a place you can see to a place you can't. And that is strictly more dangerous than any previous abstraction — because in every previous paradigm, when something went wrong, you could trace backward from the failure to the cause. In agent systems, the causal chain runs through a neural network.18See also: Perrow, Charles. Normal Accidents. 1984. Wikipedia
The new source code
In traditional programming, source code is the artifact that lets you understand what happened and why. You read the code. You trace the logic. You find the bug.
In agent programming, trajectory logs are that artifact.
A trajectory is the complete record of an agent's execution: every prompt it received, every tool it called with what arguments, every intermediate result, every decision point, every human approval or rejection. It is the flight data recorder for agent systems.
Trajectory logs are not optional infrastructure you'll add in version two. They are not "nice to have" observability. They are the source code of agent systems. Without them, you are writing software you cannot read.
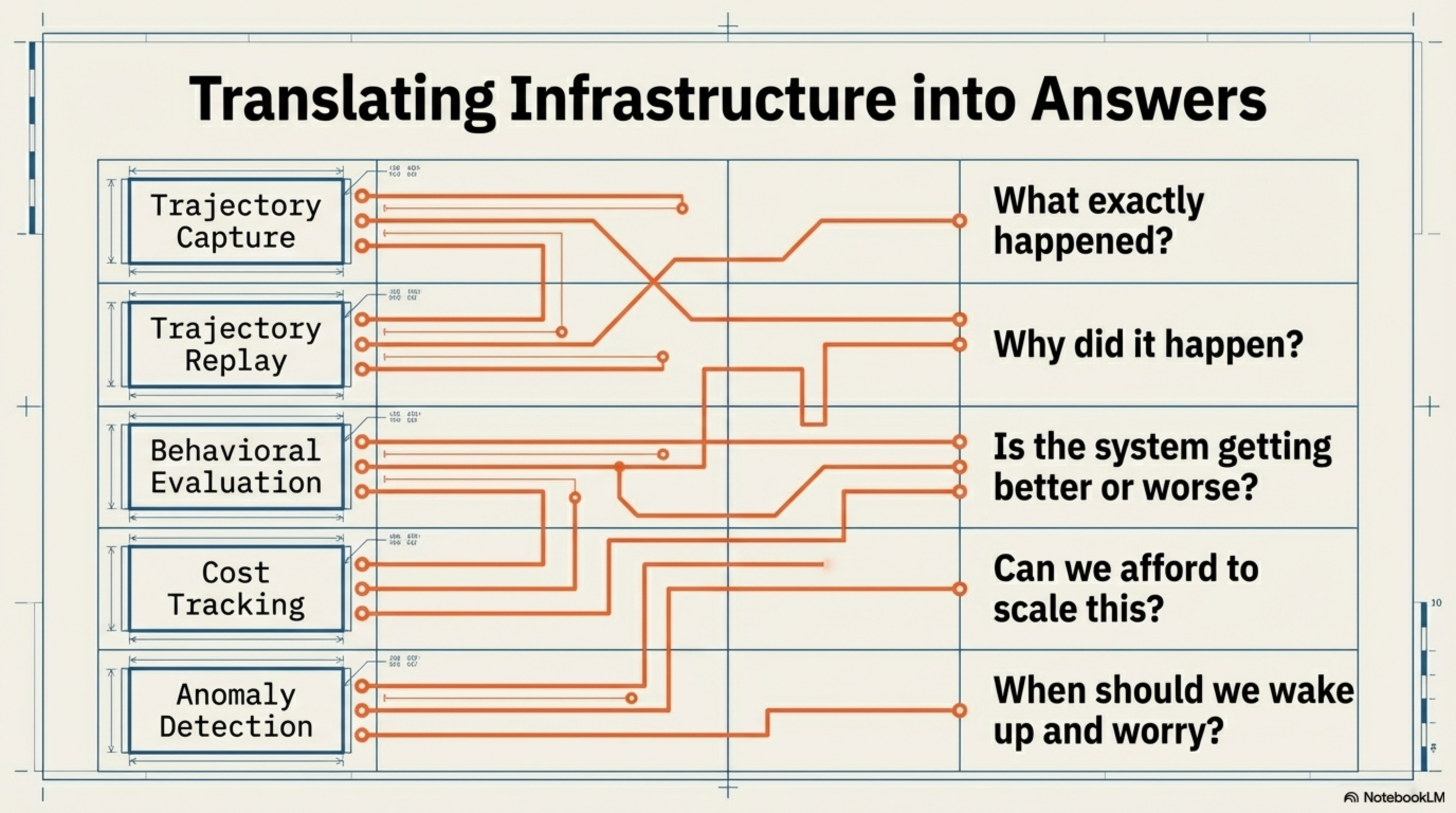
| Capability | Without it, you can't answer |
|---|---|
| Trajectory capture | "What happened?" |
| Trajectory replay | "Why did it happen?" |
| Behavioral evaluation | "Is it getting better or worse?" |
| Cost tracking | "Can we afford to scale this?" |
| Anomaly detection | "When should we wake up and worry?" |
Build this before you build your third agent. You'll thank yourself at 3 AM when your system does something unexpected — and you can see why.
For each agent in your production system, answer four questions. Any "false" is a blind spot where your next 3 AM incident will originate. This is not optional observability. This is the source code of your agent system.
// FOR EACH AGENT
can_see_input = true | false
can_see_tool_calls = true | false
can_see_decision = true | false
can_see_why = true | false
// Each false is where your next mystery lives.