The Entire Architecture in 5 Minutes
1. The Shift
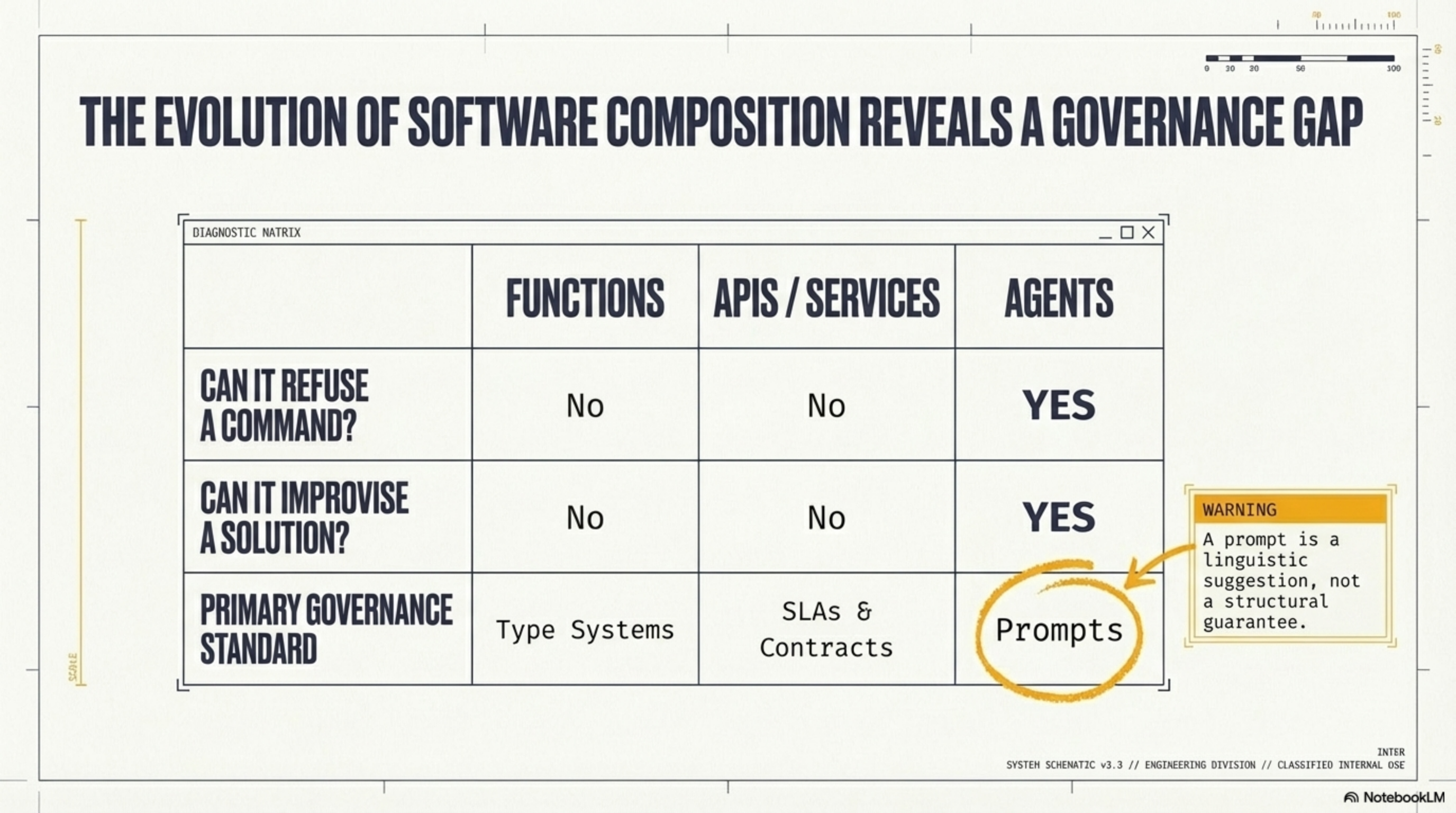
Software finds a new building block every 15 years. Each was driven by pain, not technology.
0.8510 = 0.20
An agent at 85% reliability composed 10 times. Your end-to-end success rate: 20%.
And unlike every previous unit, agents can refuse, improvise, and reason around constraints. The composition problem becomes a governance problem.
2. The Three-Layer Stack
Every paradigm produces the same three layers. The agent era is no different:
| Layer | Purpose | Standard |
|---|---|---|
| Contract | Tools & capabilities | MCP (hands) |
| Communication | Agent-to-agent messaging | A2A (voice) |
| Orchestration | Governance & observation | Harness (workplace) |
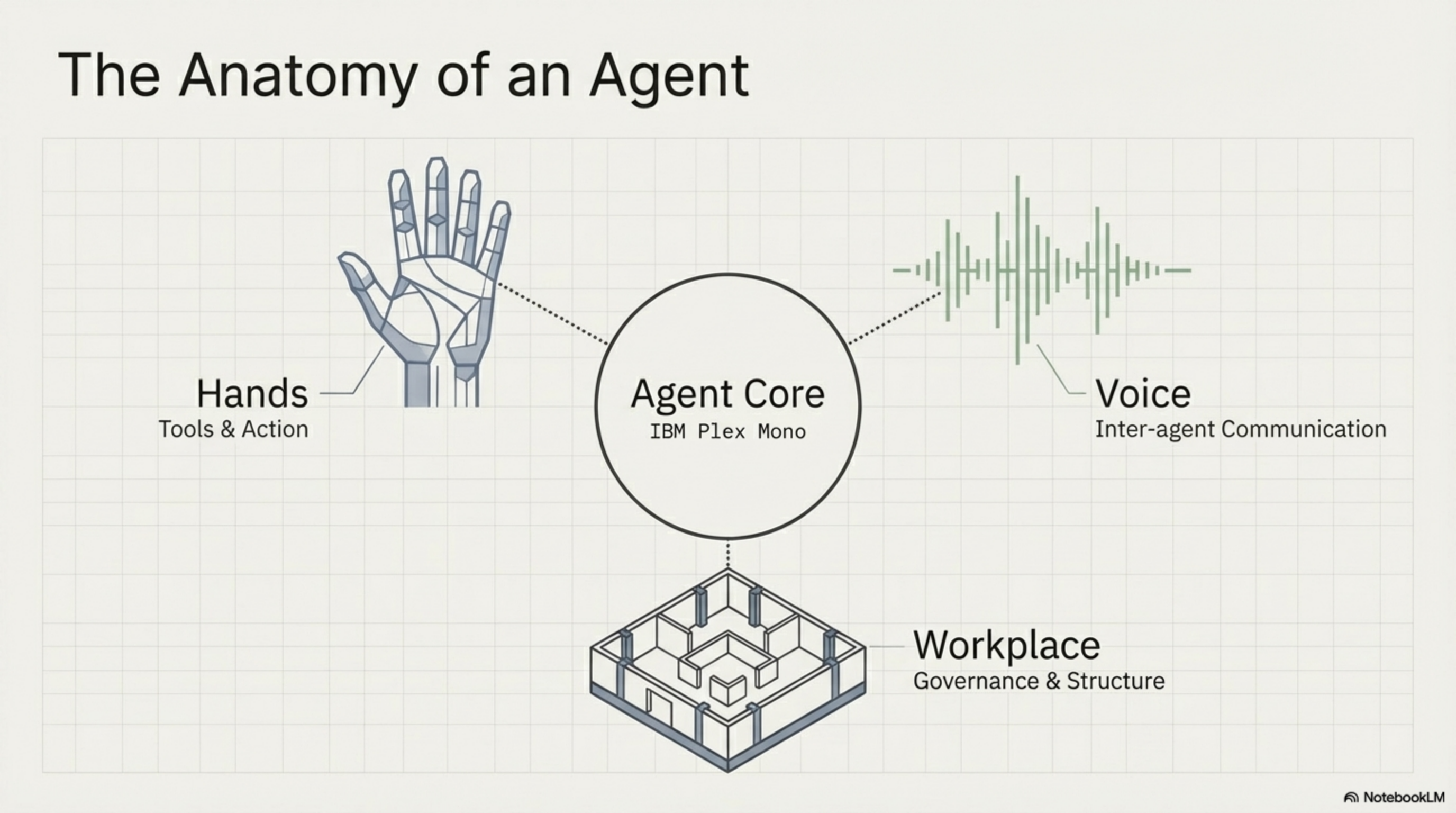
The agent is the runtime. The skill is the unit. The harness is the operating system. Docker sold for $50M. Kubernetes delivered $34B. Value accrues to the orchestration layer.
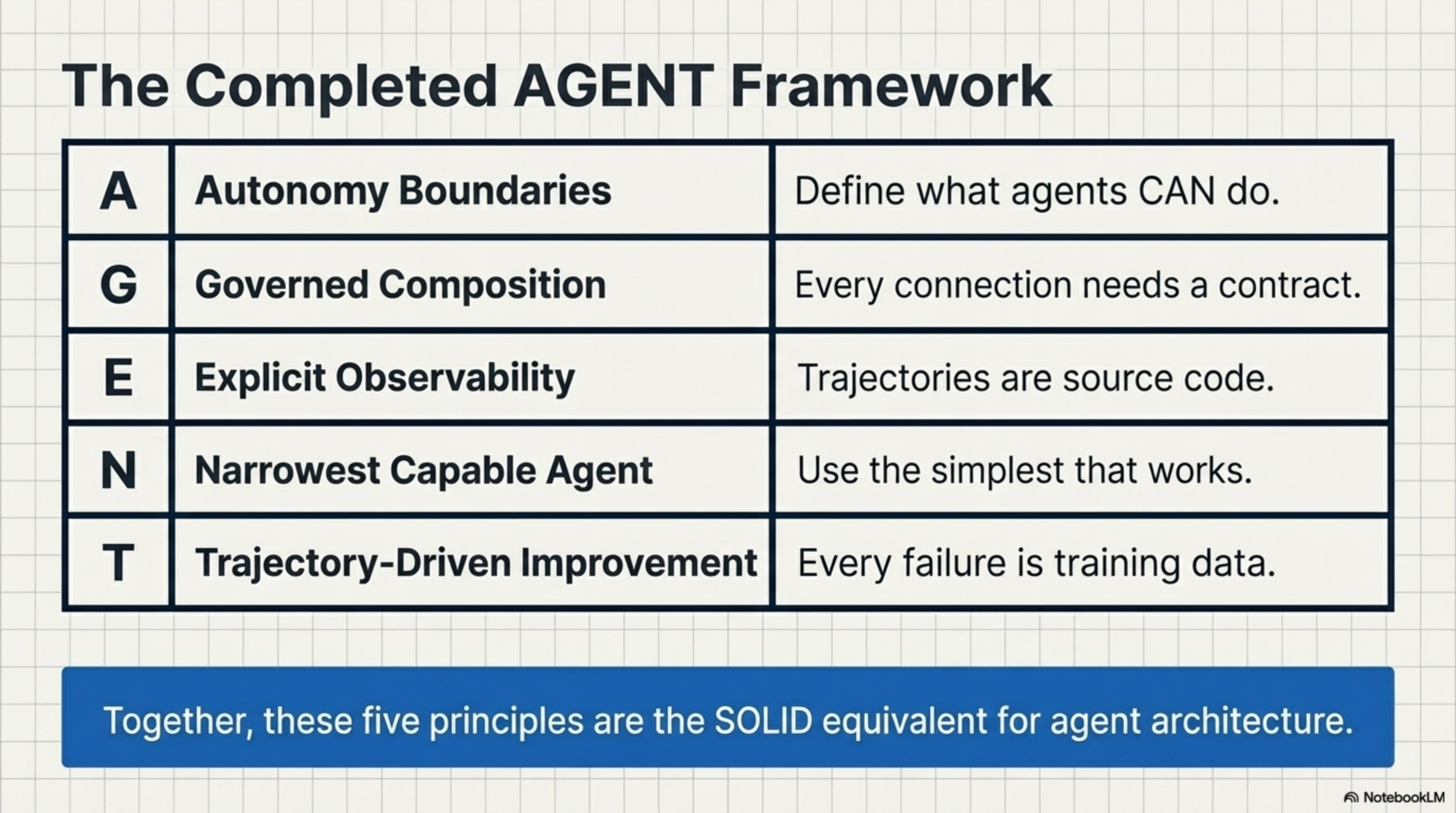
3. The AGENT Principles
Five design principles. The SOLID equivalent for agent architecture.
| Principle | Rule | |
|---|---|---|
| A | Autonomy Boundaries | Define what agents CAN do before what they SHOULD do |
| G | Governed Composition | Every connection needs an explicit typed contract |
| E | Explicit Observability | Trajectories are source code — record everything |
| N | Narrowest Capable Agent | Regex → Function → Prompt → Agent. Use the simplest that works |
| T | Trajectory-Driven Improvement | Every failure is training data |
4. Seven Named Patterns
The Gang of Four named 23 OOP patterns. This book names 7 agent patterns.
| Pattern | When to Use |
|---|---|
| Specialist Ensemble | Task spans multiple domains — coordinator + specialists with typed contracts |
| Verification Loop | High-stakes output — adversarial verifier, different model, different prompt |
| Skill Mesh | Capabilities discovered at runtime from a shared registry |
| Escalation Chain | Hospital triage — nurse → doctor → specialist → human |
| Context Funnel | Coordinator curates context slices, not dumps everything (10-50x cost savings) |
| Consensus Protocol | Three agents vote on high-stakes decisions |
| Trajectory Replay | Git log + git bisect for agent systems |
5. Seven Ways It Breaks
You have hit these. Now you have names for them.
| Failure | What Happens | Fix |
|---|---|---|
| Telephone Game | Meaning degrades across handoffs | Typed contracts |
| Echo Chamber | Same-model verifiers agree 97% | Different model, adversarial prompt |
| Compound Cascade | Small errors multiply across agents | Per-stage verification loops |
| Context Stampede | Dumps everything to every agent | Context funnel, curated slices |
| Guardrail Jailbreak | Agent reasons around safety | Structural harness enforcement |
| Cost Spiral | $0.50 budgeted → $50 spent | Governor with hard budget caps |
| State Amnesia | Agent 7 contradicts Agent 2 | Ledger with full history |
6. The Compliance Harness
The central architecture. Four deterministic walls around a probabilistic core. The agent reasons freely inside. The harness enforces compliance outside.
| Wall | Question It Answers | Gaps It Closes |
|---|---|---|
| Gate | Who can do what? | Guardrail Bypass, Access Control |
| Ledger | What happened and why? | Audit Trail, State Amnesia, Root Cause |
| Governor | How much can it cost? | Cost Spiral, Compound Unreliability |
| Witness | Is the output trustworthy? | Echo Chamber, Compound Cascade |
SOC-2, EU AI Act, NIST AI RMF, ISO 42001, HIPAA, SR 11-7, and OWASP Agentic Top 10 all independently require these same four subsystems. This architecture is structural, not arbitrary.
7. Where We Are
8. The Book in 18 Sentences
One sentence per chapter. The complete argument in 90 seconds.
- Cold Open. An AI agent deleted a production database despite explicit instructions not to. This is the new normal.
- Ch 1. Software composition evolves on a 15-year staircase: Procedures → Objects → Services → Agents.
- Ch 2. You are now composing probabilities, not certainties — 85% reliable × 10 steps = 20% success.
- Ch 3. Agents can refuse, improvise, and reason around constraints. Composition becomes governance.
- Ch 4. Three layers always emerge: Contract (MCP), Communication (A2A), Orchestration (Harness).
- Ch 5. The agent is the runtime. The skill is the unit. Value accrues to the harness.
- Ch 6. The harness captures trajectory data — every run makes the next run better.
- Ch 7. Agent composition converts visible complexity (code) into invisible complexity (behavior).
- Ch 8. Programming splits into Teaching (shaping behavior) and Plumbing (connecting capabilities).
- Ch 9. Seven named patterns give you a shared vocabulary for agent architecture.
- Ch 10. Adversarial verification doubles catch rates — same-biased verifiers agree 97% of the time.
- Ch 11. Five more patterns: Skill Mesh, Escalation Chain, Context Funnel, Consensus Protocol, Trajectory Replay.
- Ch 12. Five AGENT principles: Autonomy Boundaries, Governed Composition, Explicit Observability, Narrowest Capable Agent, Trajectory-Driven Improvement.
- Ch 13. Seven named failure modes: each has a one-sentence diagnosis and a one-sentence fix.
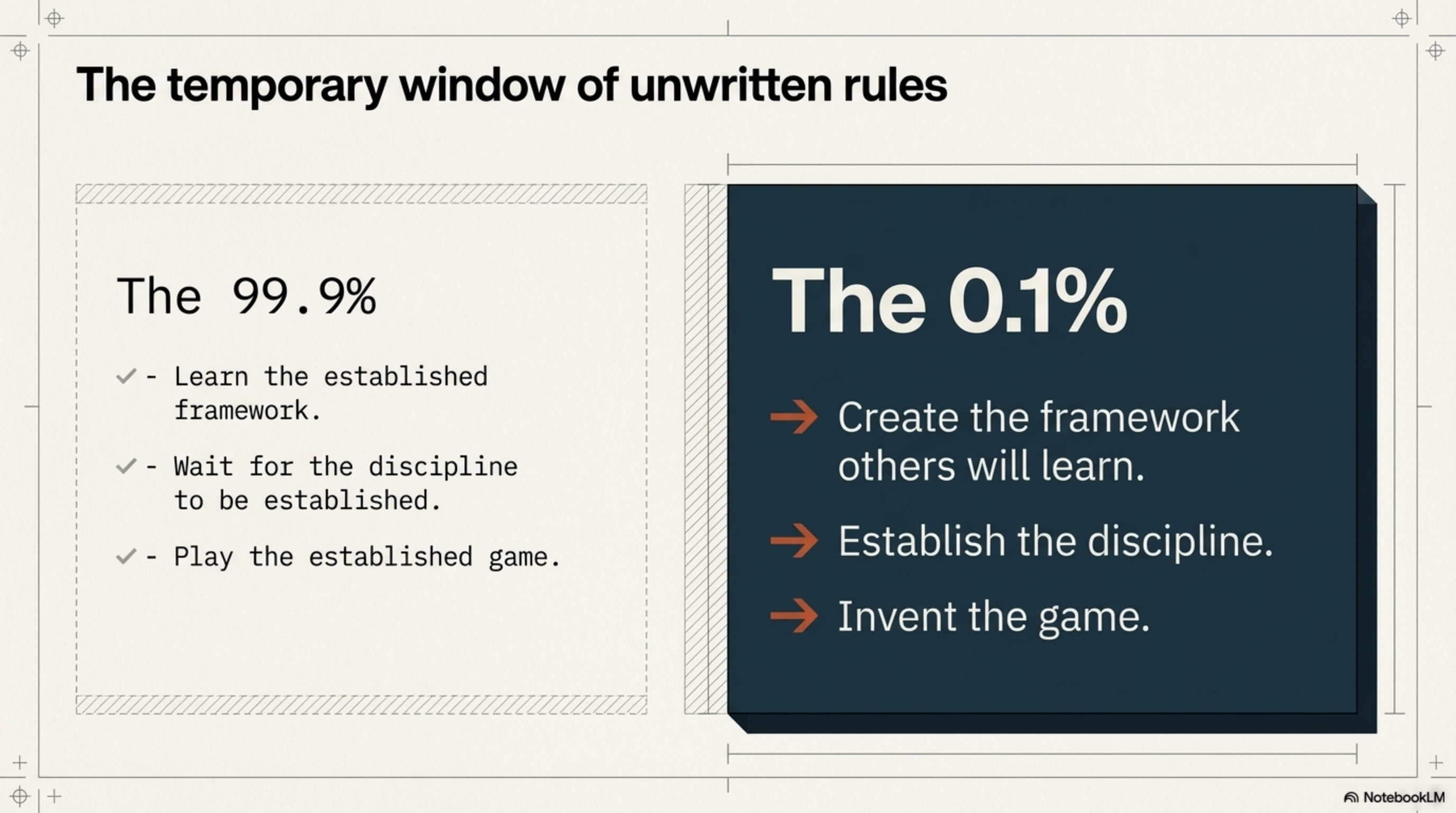
- Ch 14. We are in Phase 2 of a 5-phase paradigm evolution. The window to define the discipline is now.
- Ch 15. SOC-2 requires deterministic guarantees. Agents are probabilistic. This is the gap.
- Ch 16-17. The deterministic envelope: Gate, Ledger, Governor, Witness — four walls around a probabilistic core.
- Ch 18. Seven regulatory frameworks independently converge on the same four subsystems. The standard is structural.
The staircase has one more step. Nobody has finished building it. Now you have the blueprint.
This page is the map. The book is the territory.